Requirements
General requirements
nShield Monitor is delivered in the following formats:
-
Open Virtual Appliance (OVA)
-
Microsoft Hyper-V
Both formats include:
-
A 64-bit Linux-based OS
-
Open VMware Tools (OVT)
| By default, OVT service is DISABLED. A system administrator can choose to ENABLE OVT from the CLI. For details, refer to Service Commands. |
Hypervisor compatibility
The OVA can be installed on the following virtual platforms:
-
vSphere ESXi 6.0
-
vSphere ESXi 6.5
-
VMware Workstation 12
-
VMware Workstation 14
-
VMware Fusion 10
-
Oracle VirtualBox 6.0
The Hyper-V image can be installed on the following virtual platforms:
-
Microsoft Hyper-V
-
Microsoft Azure
Server requirements
-
Must support 64 bit OS
-
CPU: 2 cores of 2.0GHz multicore CPU (can be increased as needed)
-
Memory: 8GB dedicated memory for nShield Monitor (can be increased)
-
Network: Single network attached interface to bridged or physical network
Size on disk:
-
Thin provisioned: 2.3 GB (OVA) / 3.3 GB (Hyper-V)
-
Thick provisioned: 326.0 GB (OVA)
Centralized monitoring
When monitoring an estate of HSMs (that is, more than one HSM), reduce data duplication by keeping your data in as few places as possible.
| Multiple instances of your data may be required due to your organization’s external requirements. For example, due to regulatory issues. |
Client workstation
The client workstation is any Apple or Microsoft Windows workstation that has network connections to nShield Monitor. A supported browser (WebUI access) or SSH client (CLI access) that can access nShield Monitor is required.
The client workstation can perform various configuration, administrative tasks or group management tasks based upon defined roles.
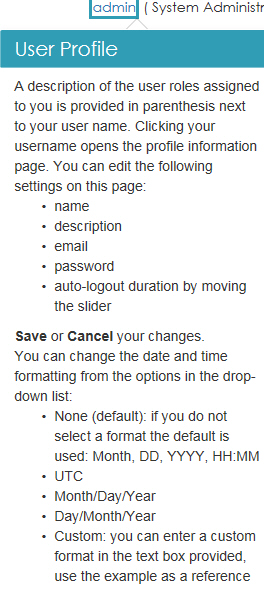
Role based access
nShield Monitor supports role-based access.
Each nShield Monitor user role is associated with a predefined set of tasks. This ensures that a user with a specific role can perform only those tasks that are allowed by that role. For example, if a user is assigned the role of group manager, the user cannot perform administrative tasks, such as creating users. Role-based access adds a level of security to the configuration and administration of nShield Monitor.
The following credential schemes are supported:
-
nShield Monitor’s own credential scheme, see Creating Users.
-
Active Directory credentials, see Active Directory authentication.
Active Directory authentication is set up by mapping Active Directory groups to nShield Monitor roles.
| For users whose credentials were imported from Active Directory, Configuration > Security shows their own credentials in and for nShield Monitor. Changes made to passwords in nShield Monitor are not ported back automatically to the Active Directory server. |
| Users who are Active Directory administrators have no access or visibility to the credentials of other Active Directory users through Configuration > Security. |
User roles
The nShield Monitor role based administration model has the following role type:
-
Auditor
-
Administrator
-
Group Manager
Users can be assigned to more that one role. For example, a user could be both am Administration and as a Group Manager. This user is then able to perform tasks related to both an the administrator role and a group manager role.
For example, you could create users with the following combinations of permissions:
-
User #1: administrator and group permissions
-
User #2: auditor only
-
User #3: group manager only
The nShield Monitor UI is role sensitive, and the pages displayed are dependent upon the role of the user.
Auditor
Auditors have complete visibility into nShield Monitor; however, they cannot modify any setting in nShield Monitor or on the HSMs.
| Auditors cannot be Administrators or Group Managers. |
The auditor role is for visibility purposes.
Administrator
| Administrators are required to have sufficient knowledge of networks, various operating systems, and general system administration tasks such as configuring IP addresses, backing up systems, and using the console interface. |
The Administrator is responsible for:
-
User management, including creating new users, and deleting users who do not have any roles assigned to them
-
Assigning administrator or group manager roles to users
-
Network configuration
-
System configuration
-
Upgrading the system
-
License management
-
Security configuration
-
Group management
-
Event notification (syslog, SNMP and email) management
-
Enabling the Open VMware Tools Service
Group Manager
Group Managers are required to have sufficient knowledge and understanding of:
-
The importance of the data and devices that they manage
-
Corporate policies with respect to data dissemination
-
Corporate policies with respect to problem resolution
The Group manager is responsible for monitoring and understanding the following:
-
The command instruction usage
-
HSM utilization
-
HSM health
-
Event triggers in assigned groups
-
Event logging and report generation in assigned groups
-
Configuring event notification via email in assigned group
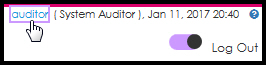
Accessing the User Guide
Online Help is available to all user role types.
| While Online Help is enabled, you cannot perform any actions on the GUI. |
-
Log on as Administrator, Group Manager, or Auditor.
-
Locate the toggle switch in the upper right corner of the screen.
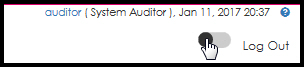
-
Slide the toggle switch to the right.
Online Help is enabled.
Fields surrounded by a colored box contain help.
-
Click a field to open the help text pop-up window. For example: