Integrate the MS SQL Server with the Entrust CSP Vault
For reference, see Microsoft SQL Server Manual Installation and Configuration.
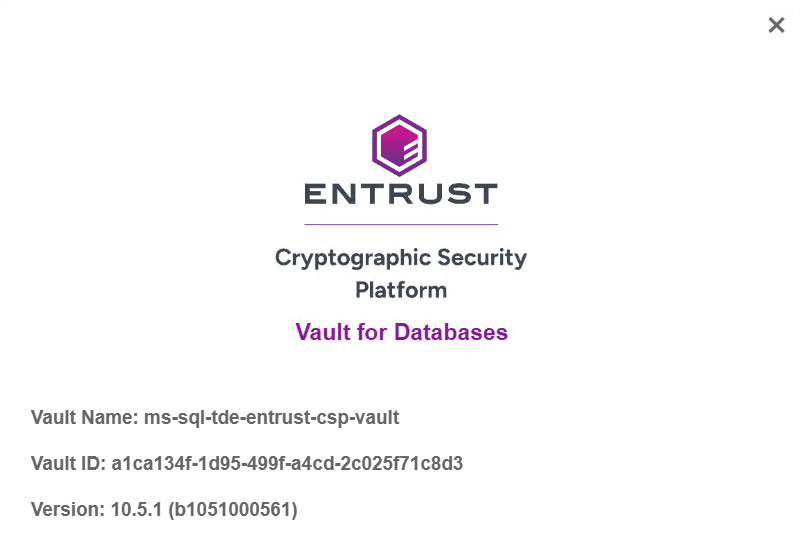
Get the vault information
-
Sign in to the MS SQL Server host.
-
From the MS SQL Server host, sign in to your vault web GUI.
-
In the top left, under Administrator, select About from the drop-down menu.
For example:
-
Make a note of the Vault ID.
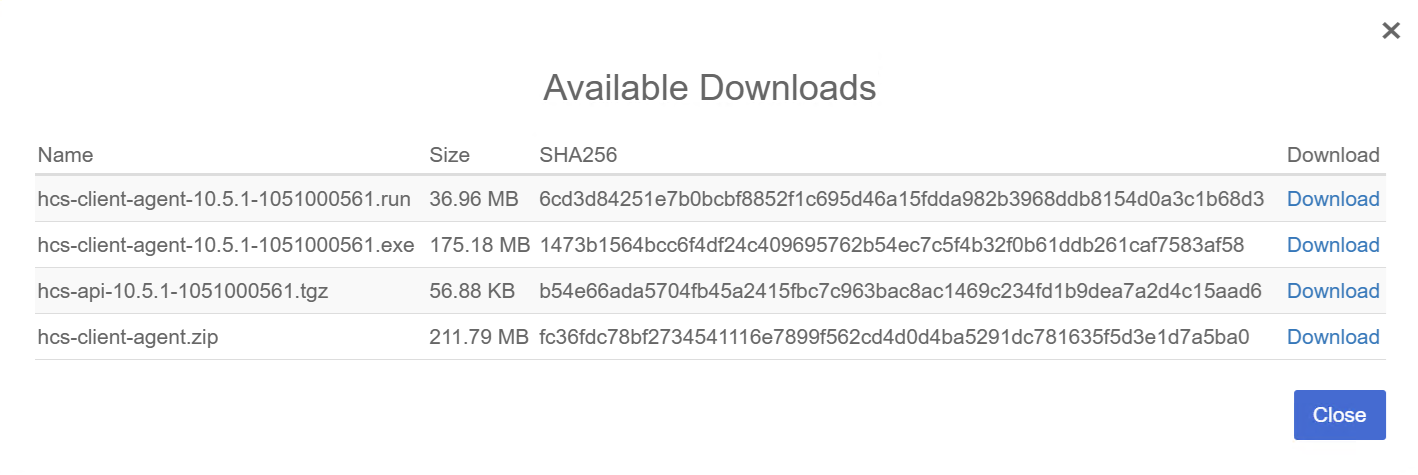
Install the policy agent client on the MS SQL Server host
-
Sign in to the MS SQL Server host.
-
From the MS SQL Server host, sign in to your vault web GUI.
-
In the toolbar select WORKLOADS.
-
Select Actions, then select Download Policy Agent from the drop-down menu.
For example:
-
Select Download next to the
hcs-client-agent-<version>.exefile.Alternatively, download the
hcs-client-agent.zipfile and then extract the Windows executable. -
Select Close.
-
Run the downloaded file,
hcs-client-agent-<version>.exe.Alternatively, open the
ZIPfile and navigate to thehcs-client-agent\windowsfolder and then run the executable. -
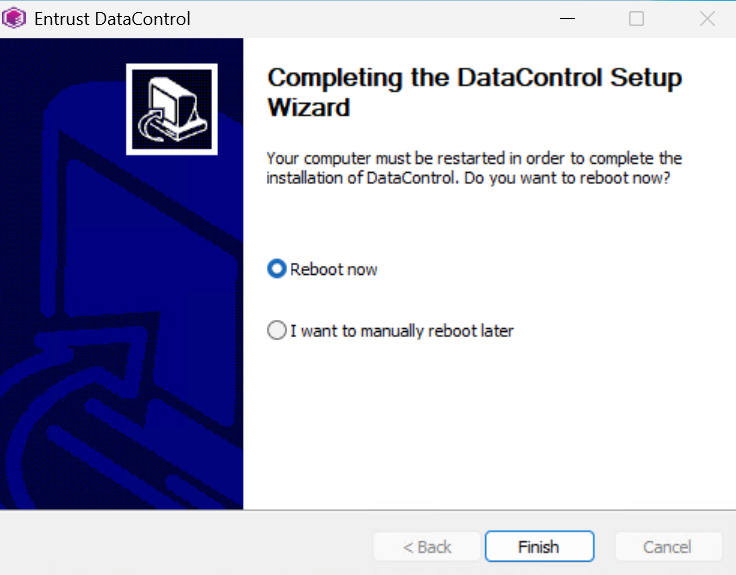
Complete the install process using the default options.
-
Upon completion, select Reboot now, then select Finish.
Register the MS SQL Server with your vault
-
On the MS SQL Server host, sign in to your vault web GUI.
-
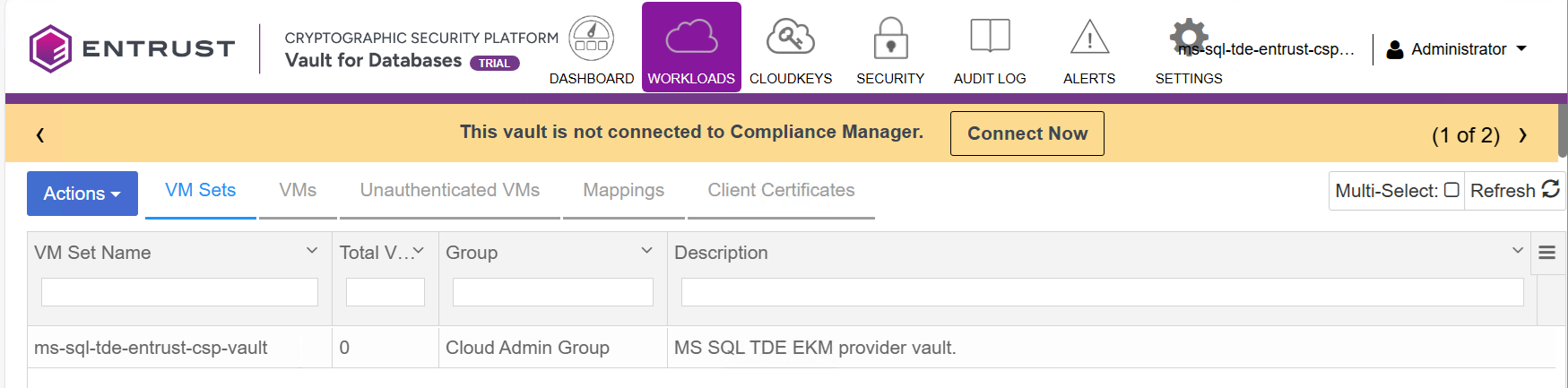
In the toolbar, select WORKLOADS.
-
Select Actions, then select Create New Cloud VM Set from the drop-down menu.
-
In the Create Cloud VM set window, enter a Name and Description, then select Create and Close.
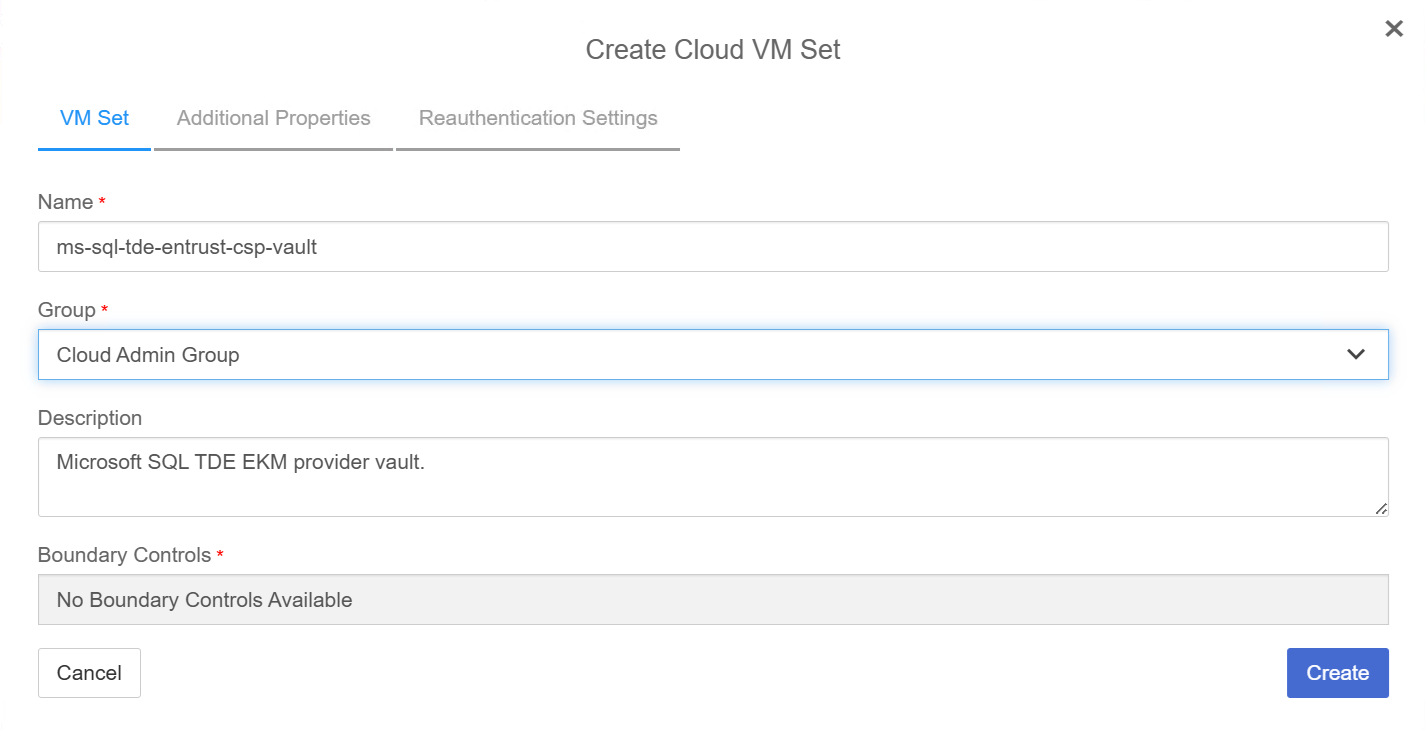
The new cloud VM set appears.
-
Select the Start menu in the MS SQL Server host and navigate to Entrust DataControl.
-
Select Register.
-
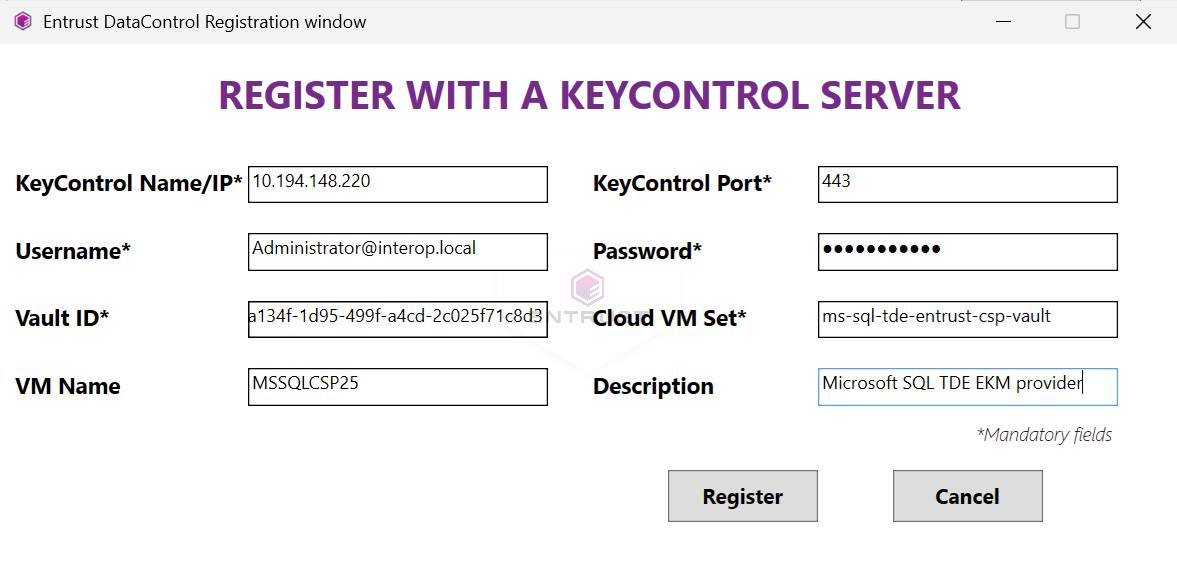
In the Register window, enter the information as follows, then select Register and OK.
For example:
Parameter Value Name / IP
First node of the Entrust CSP Vault cluster
Username
User created in Configure the Entrust CSP Vault
Password
User created in Configure the Entrust CSP Vault
Vault ID
Cloud VM set
Name of cloud VM set created above
-
After registration succeeds, select OK.
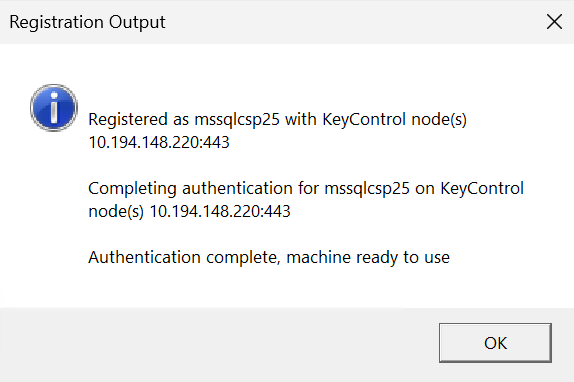
The Entrust DataControl window now shows STATUS Connected.
-
Close the window.

Enable TDE on the MS SQL Server
-
On the MS SQL Server host, open a command window as an administrator.
-
Run the following command to enable TDE on the server:
C:\Users\Administrator.INTEROP>hcl tde status TDE is not enabled on this VM C:\Users\Administrator.INTEROP>hcl tde enable Enabling tde will change permissions of some Files. Do you want to proceed? (y/n) y If you are enabling TDE for an Oracle database, follow the steps mentioned below from the Administritor Guide. "Administration Guide > KeyControl Vault for Databases > KeyControl with Oracle TDE > Configuring the Oracle Server Database" C:\Users\Administrator.INTEROP>hcl tde status TDE is enabled on this VM C:\Users\Administrator.INTEROP>hcl status Summary ------------------------------------------------------------------------------- KeyControl: 10.194.148.220:443 KeyControl list: 10.194.148.220:443 Vault ID: a1ca134f-1d95-499f-a4cd-2c025f71c8d3 Status: Connected Last heartbeat: Mon Apr 6 11:11:05 2026 (successful) Certificate Expiration: Apr 6 14:42:47 2027 GMT -
Sign in to your vault web GUI.
-
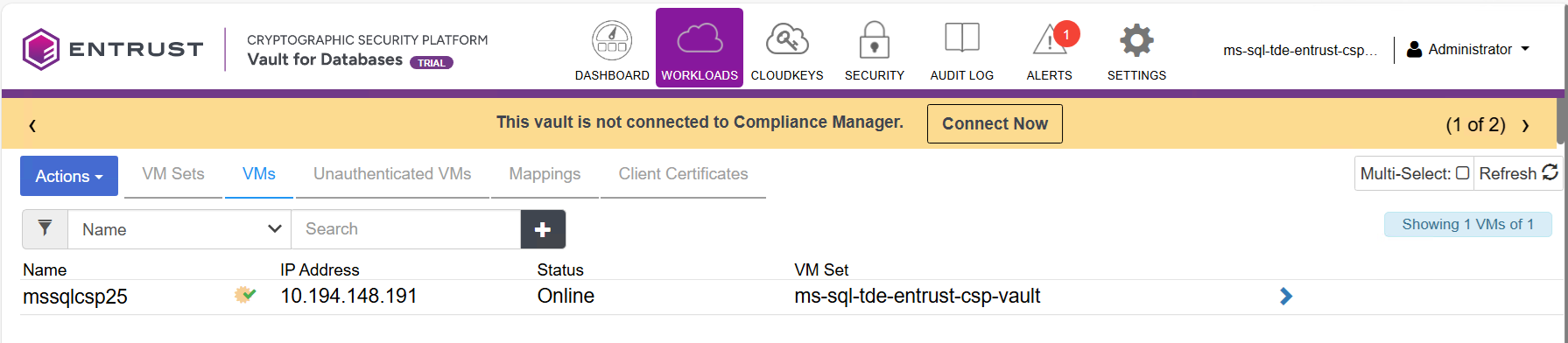
In the toolbar select WORKLOADS, then select the VM tab.
The Microsoft SQL Server host now appears.
Create a TDE database keyset to hold the cloud keys
-
On the MS SQL Server host, sign in to your vault web GUI.
-
In the toolbar select CLOUDKEYS.
-
Select Actions, then select Create Key Set from the drop-down menu.
-
In the Create Key Set window, on the Details tab, enter the details as follows, then select Continue.
For example:
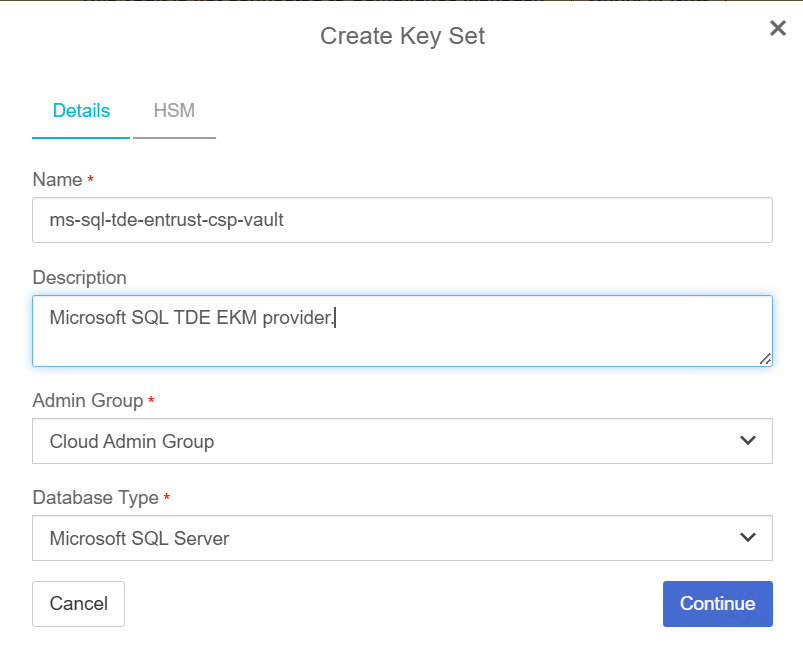
-
Enter the HSM information, if provisioned, then select Apply.
-
After the keyset is successfully created, select Close.
Create the database connector
-
On the MS SQL Server host sign in to your vault web GUI.
-
In the toolbar, select CLOUDKEYS, then select the Key Sets tab.
-
Select your keyset created in Create a TDE database keyset to hold the cloud keys.
-
Scroll down and select the Database Connectors tab.
-
Select Create Connector Now.
-
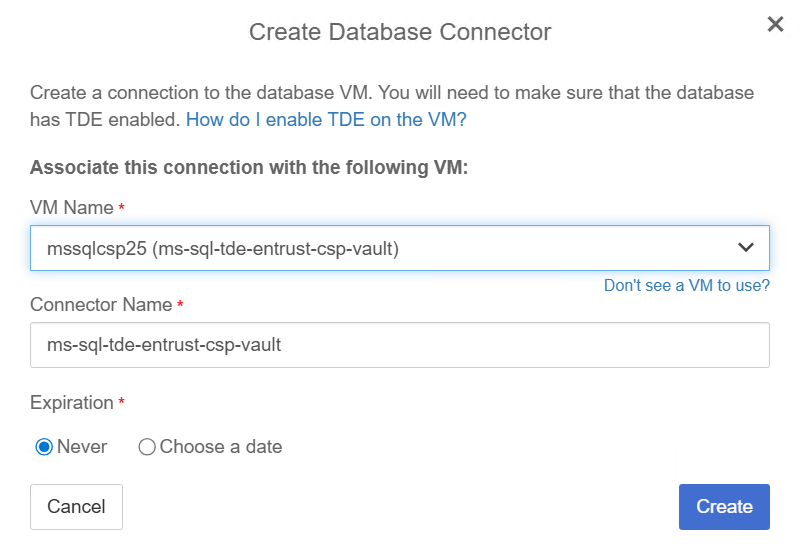
In the Create Database Connector window, select your Microsoft SQL Server host from the drop-down menu.
-
Enter a name and select the expiration, then select Create. In this integration, we configure the connector to never expire.
For example:
-
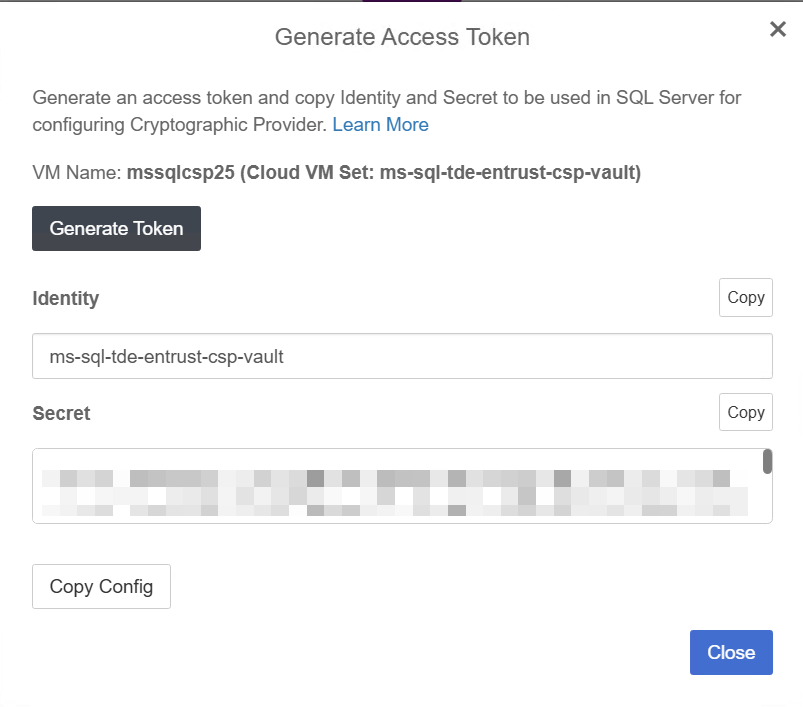
Check the box next to the Database Connector created, then, from the Actions drop-down menu, select Generate Access Token.
-
In the Generate Access Token window, select Generate Token.
The access token is generated.
-
Copy and save the Identity and Secret.
For example:
Load the EKM provider on Microsoft SQL Server
-
Launch Microsoft SQL Server Management Studio and connect to the SQL Server.
-
Run the following query to enable the EKM provider:
USE master GO -- Enable EKM provider sp_configure 'show advanced options', 1 ; GO RECONFIGURE; GO sp_configure 'EKM provider enabled', 1 ; GO RECONFIGURE; GO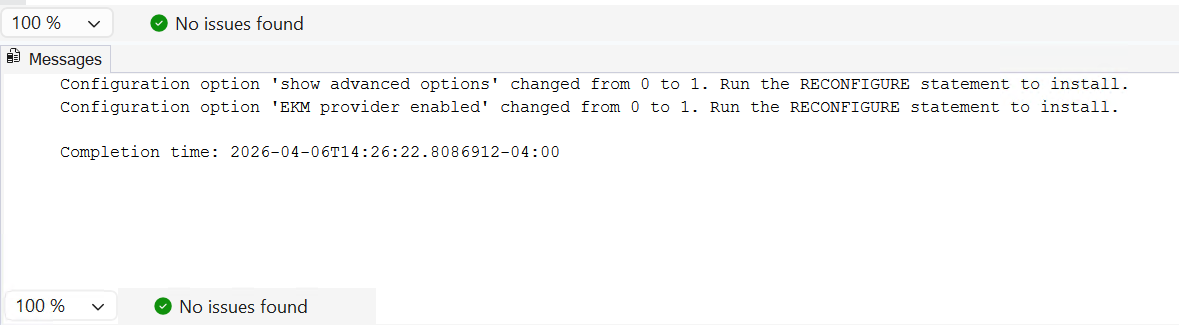
-
Run the following query to load the EKM provider library:
-- Load cryptographic provider CREATE CRYPTOGRAPHIC PROVIDER Entrust_CSP_Vault FROM FILE = 'C:\Program Files\hcs\bin\htsqlekm_provider.dll'; GO -
Using the Identity and Secret from section Create the database connector, create a credential file in JSON format. Place this file where it is accessible to the SQL Server, for example
C:\Users\Administrator\sqlcred.conf.{ "identity" : "ms-sql-tde-entrust-csp-vault", "secret" : "WsZdrsP0mpbrTVtZSLGs6sUOZylq0cB0FmpyNl7nNwiuN3PbjSThQj59eACZCg3IYZo/dtFn5Acr6FceJ+a/NAAhqS7keQ0T5cgXswjHVZz4gYrkqTPfMeUI8vM6z79E6qvVp/Fyr840nlhzle1nSKiVohD85Dmued40dRvOqFy4iKuNWEwBEk9bs35P1La1iYz1ANDm31QH0akhT6+C9sONOTsHSzs1JoZphNnPDN2PULJVIXkdo+yhbF+xBfW3P6N4JaQWK1aL09qIin/dX+Y/nBmeXbknKyiBJendO5jjSrRFMvkhZBNjEAlKdUucIaPBpoe2m6~NRT3gkHo/jSJ6dgKy9GpvcylgufDLzfz8jEfZuLKenfhSp5E75mJMfYqApuhBK56GfqpH+sp2NmhSdXyMcixE+6u+HLy/3VNTnf9HezmrFMPNq1NF6NZBB9dQyz6KBfZ9zjPpNu6H2kJFbH3jwkzYkfvnKBM9vC+ki25RTWNMOTQchf43LC3vaxup3QGNcBfUWqXFWxsmTSkSY04K3B+oDXVr77IoOGT59Fi6LhHv4ncEMr5w1dK2svRyf8W8iRebi0d1VsKbtgPg4KwoWdMp7U/VRxon16BeXvZgJ3YUFdsaCZL3eghjNFEWOHP/v33Sx8EtzL53oT/5xCJprze1U=" } -
Run the following query to create login credentials for the administrator:
-- Create credential for system administrator CREATE CREDENTIAL sa_entrust_csp_vault WITH IDENTITY = 'file:C:\Users\Administrator\sqlcred.conf', SECRET = 'ignore' FOR CRYPTOGRAPHIC PROVIDER Entrust_CSP_Vault; GO -- Add this credential to the system administrator login ALTER LOGIN [INTEROP\Administrator] ADD CREDENTIAL "sa_entrust_csp_vault"; GOWe recommend pointing to the sqlcred.conffile in the query instead of simply listing the actual identity and secret. The former is required for SQL Server clusters.
Create a master key in the Entrust CSP vault
-
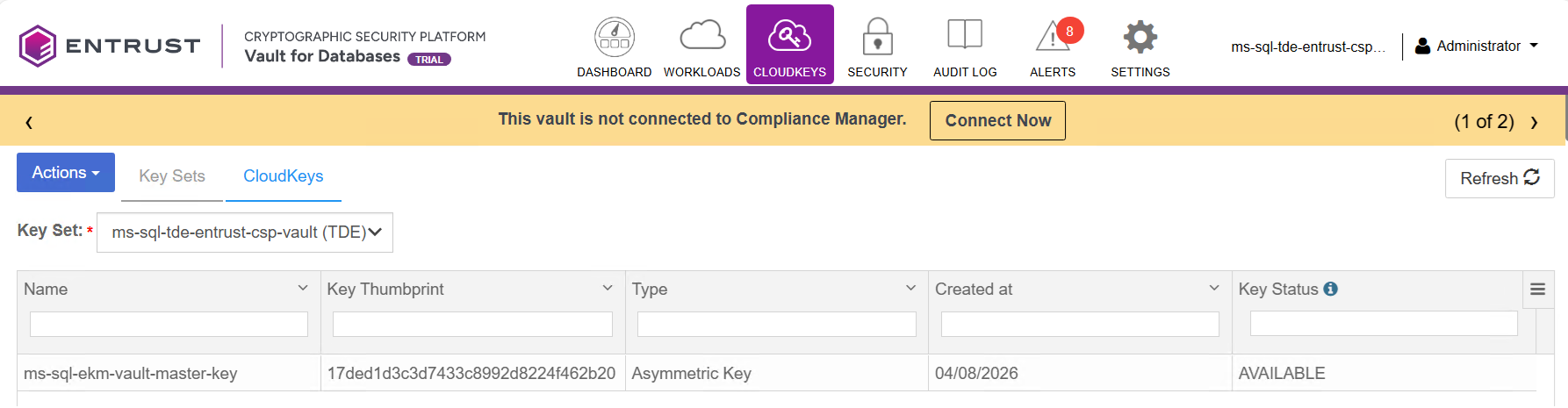
On the MS SQL Server host, sign in to your vault web GUI.
-
In the toolbar select CLOUDKEYS, then select the Cloud Keys tab.
-
In the Key Set drop-down menu, select your keyset created in Create a TDE database keyset to hold the cloud keys.
-
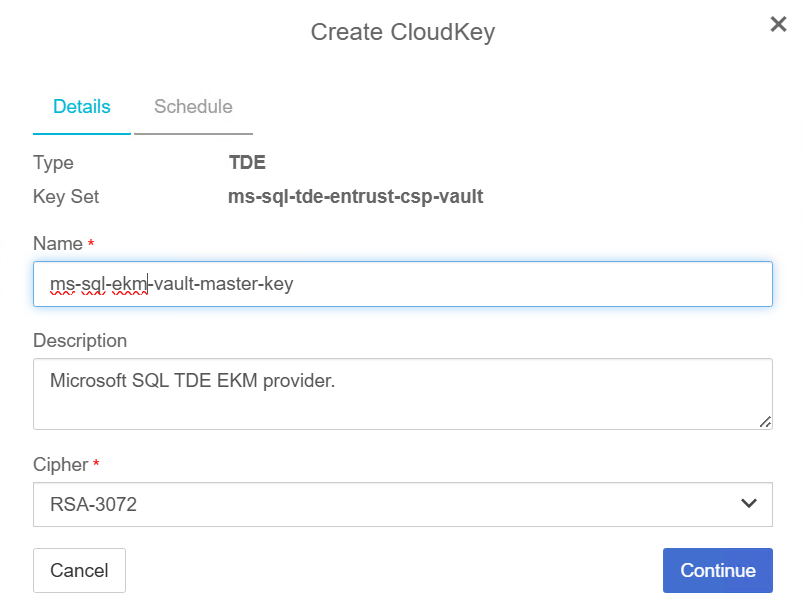
Select Actions > Create CloudKey.
-
In the Create CloudKey window Details tab, enter a Name and Description.
-
Select the Cypher per your application requirements, then select Continue.
SQL Server supports a maximum of 3072 bits for the Cypher. For example:
-
In the Schedule tab, select the required options, then select Apply and Close.
The master key is created.
Create the TDE key and login on Microsoft SQL Server
-
Launch Microsoft SQL Server Management Studio and connect to the SQL Server.
-
Run the following query to create a TDE key protected by the EKM provider vault master key created in Create a master key in the Entrust CSP vault.
USE master; CREATE ASYMMETRIC KEY TDE_Key FROM PROVIDER Entrust_CSP_Vault WITH PROVIDER_KEY_NAME = 'ms-sql-ekm-vault-master-key', CREATION_DISPOSITION = OPEN_EXISTING; GO -
Run the following query to create a login for the TDE user:
-- Create login for TDE user CREATE LOGIN TDE_Login FROM ASYMMETRIC KEY TDE_Key ; GO -
Run the following query to create a credential for the TDE login:
-- Create credential for the TDE user CREATE CREDENTIAL tde_entrust_csp_vault WITH IDENTITY = 'file:C:\Users\Administrator\sqlcred.conf', SECRET = 'ignore' FOR CRYPTOGRAPHIC PROVIDER Entrust_CSP_Vault; GO -- Add this credential to the TDE user login ALTER LOGIN TDE_Login ADD CREDENTIAL "tde_entrust_csp_vault"; GO