Introduction
|
Entrust KeyControl has been rebranded as the Entrust Cryptographic Security Platform (CSP) Key Manager. The Entrust CSP Key Manager continues to provide a comprehensive solution for discovering and managing the lifecycles of cryptographic keys, secrets, certificates, tokens, libraries, protocols, and configurations:
Because the Entrust integrations are tested against specific product versions, this guide is still branded as a "KeyControl" integration. It was tested against a pre-CSP version of KeyControl. Exercise caution when using an Entrust Integration Guide with a product version that does not match the tested version, because your version might not function in exactly the same way. Entrust cannot guarantee the success of integrations in configurations other than those indicated in the guide. This guide remains on the website for customers using pre-CSP versions of KeyControl. |
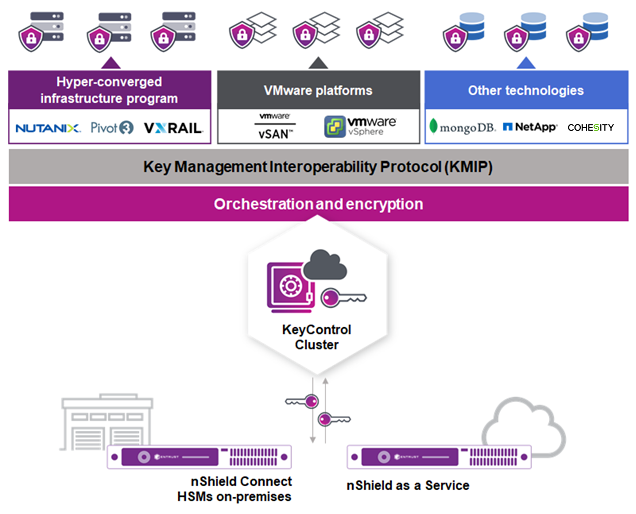
This document describes the integration of a Cohesity DataPlatform with the Entrust KeyControl Key Management Solution (KMS). Entrust KeyControl can serve as a KMS to a Cohesity cluster using the open standard Key Management Interoperability Protocol (KMIP).
Mutual authentication of each entity is performed using X.509 certificates over a Transport Layer Security (TLS) secure channel.
After deploying and configuring Entrust KeyControl, a KMS certificate is automatically generated and signed by the internal Certificate Authority (CA). The internal CA generates the X.509 client certificate that is uploaded to the Cohesity cluster for authentication.
If your organization mandates all certificates to be signed by a specific CA, KeyControl can use your organization’s CA to sign its certificate.
Once configured, the Cohesity cluster will request a Key Encryption Key (KEK) from KeyControl for the entire cluster. This KEK securely wraps (encrypt/decrypt) the Data Encryption Keys (DEKs) created and stored locally in the Cohesity cluster. The DEKs are used to encrypt and decrypt the data in the Cohesity cluster. Cohesity retrieves the KEKs from KeyControl after a reboot or a restart of the keychain service. If KeyControl is unavailable, the data in the Cluster and Storage Domains will remain encrypted and inaccessible.
Documents to read first
This guide describes how to configure the Entrust KeyControl server as a KMS in Cohesity.
To install and configure the Entrust KeyControl server cluster, see KeyControl Installation and Upgrade Guide. For information on configuring Entrust KeyControl as a KMIP server, see KeyControl KMIP Vault Overview.
Also refer to the Cohesity online documentation.
Requirements
-
Entrust KeyControl version 5.4 or later.
An Entrust KeyControl license is required for the installation. You can obtain this license from your Entrust KeyControl account team or through Entrust KeyControl customer support.
-
Cohesity DataProtect version 6.8.2 or later.
A Cohesity license is required for the installation. You can obtain this license from your Cohesity account team or through Cohesity customer support.
| Entrust recommends that you allow only unprivileged connections unless you are performing administrative tasks. |
High-availability considerations
Entrust KeyControl uses an active-active deployment, which provides high-availability capability to manage encryption keys. Entrust recommends this deployment configuration. In an active-active cluster, changes made to any KeyControl node in the cluster are automatically reflected on all nodes in the cluster. For information about Entrust KeyControl, see the Entrust KeyControl Product Overview.